Text writing pen penetration testing


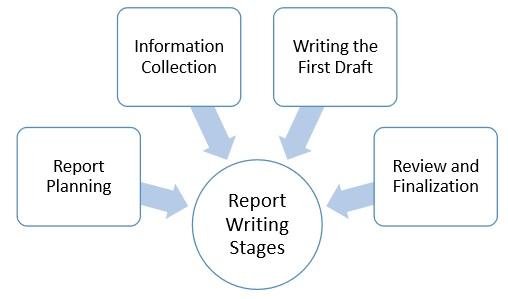
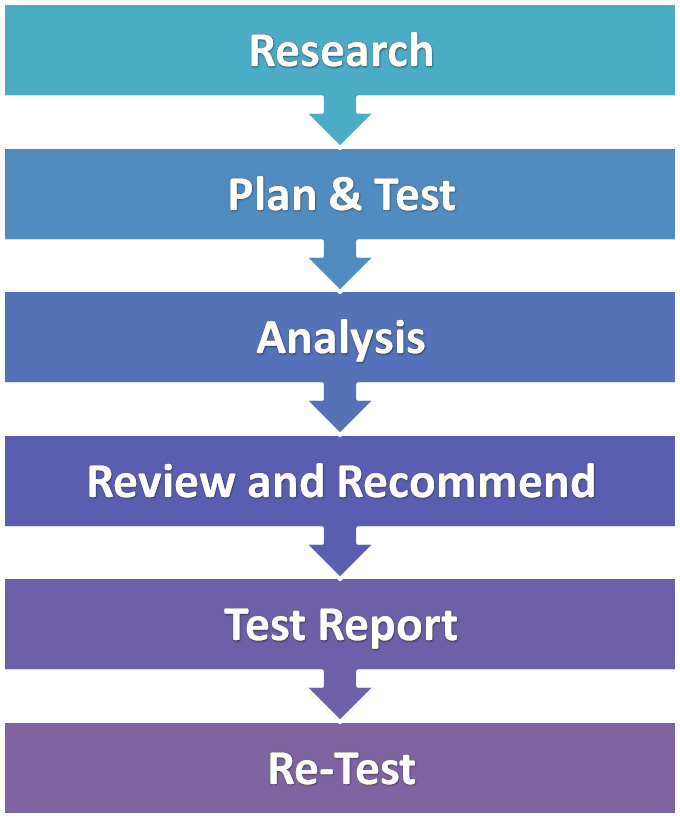
Writing a penetration testing report is an art that needs to be learned to make . Pen Tester needs to make sure that sufficient time is allotted in the project plan.
7 girls are looking for a partner for sex today Watch



Carly Age: 28. ** Petitie Women**Hello my name is EmilyEntfliehe dem Alltag und geniesse pure leidenschalf mit miryour so personal Independent female escort based in the heart of India, Delhi

Skye Age: 28. We offer streaming porn videos, downloadable DVDs, photo albums, and the number free sex community on the net.I will be happy to write you back hope to hear from you soon.You can reach me by phone can write short messages from or you can contact my mail address.
Penetration testing was much like taking a battering ram to the door of the fortress . is it harder to conduct a pen test with that many devices and end points? may be required in order to write a workable exploit code,” Xiao said. fruits like default credentials or plain text login protocols, like telnet, are not.

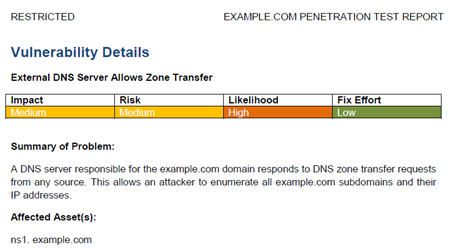
The Art of Writing Penetration Test Reports Learning to explain pen test findings in a clear and concise way is an art form, and one . I've seen this happen to extreme levels of detail, such as what font size and line spacing.










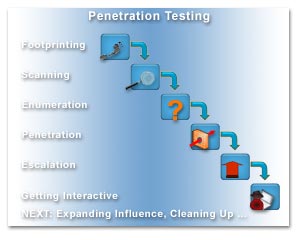
Penetration test
Description:History[ edit ] This section may have been copied and pasted from another location, possibly in violation of Wikipedia's copyright policy. Please review the source and remedy this by editing this article to remove any non-free copyrighted content and attributing free content correctly, or flagging the content for deletion. Please be sure that the supposed source of the copyright violation is not itself a Wikipedia mirror. December By the mid s, growing popularity of time-sharing computer systems that made resources accessible over communications lines created new security concerns.




























User Comments 2
Post a comment
Comment: